Welcome back to another informative article by SecuringNinja. Today we will explain the 7 most common types of cyber attacks that cyber criminals use everyday. Fear not, we will also share tips and tricks to protect against these types of cyber attacks.
Cyber criminals are continuously evolving their tactics and coming up with ever more creative ways to steal your personal information. Despite this constant evolution of tactics, there have been consistent trends in the types of attacks cyber criminals use.
The following 7 types of cyber attacks are some of the most common, and also the most dangerous.
- Phishing Attack
- Man-in-the-middle Attack
- SQL Injection Attack
- Distributed Denial of Service (DDoS)
- Password Attack
- Cross-Site Scripting (XSS)
- Ransomware
Sounds scary right? Don’t worry. We are going to take a closer look at each type of attack, and show you some simple tricks for protecting yourself.
What is a phishing attack?
The first attack we will look at is a phishing attack. I’m sure you’ve already received quite a few phishing emails yourself, but lets take a look at what a phishing attack looks like.
A phishing attack is type of social engineering attack that cybercriminals use in order to extract information from you, or get you to take an action you normally would not take. This kind of attack typically begins with an email but may also come in the form of a phone call, or SMS message.
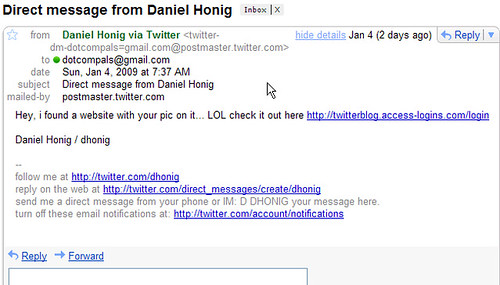
The above example claims there is a picture of you on the linked website. Clicking the link leads to an innocent looking Twitter login form. Except this login form is actually controlled by the attackers. As soon as you submit your credentials the attackers can now login to your real Twitter account.
Cyber criminals will use a variety of psychological tricks to get you to click their link and enter your information. The example above is hoping to stir your curiosity enough that you just have to see this picture of you. Other techniques attempt to pressure you with a stressful situation, such as an impending account lock out.
While generalized phishing attacks hit almost everyone’s inbox at one point or another, there is another type of phishing attack that is much more difficult to detect.
Spear phishing attack
In a spear phishing attack, rather than sending generic phishing emails to a large mailing list of potential victims, cyber criminals will carefully research their target, their stressors, their personality, etc. and then send a very carefully crafted, and convincing, email to the victim.
Spear phishing attacks typically target individuals in high level positions such as the CEO or those with access to banking information.
Cyber criminals may also include information gathered from public sources, known as OSINT, to make the message that much more convincing. For example knowing that the CEO is currently traveling in Europe adds an extra layer of authenticity to the message.
How to protect against phishing attacks
Phishing attacks have only become more sophisticated and more difficult to detect over the years. However, there are still some common red flags that will identify phishing attempts.
- Hover over links to check that they go where you expect.
- Verify the sender and their email address.
- Is this kind of request typical of this sender?
- When in doubt call the sender and verify the request.
These simple tips will protect you against most common phishing attacks. Remember, security is a mind set and you must remain vigilant!
What is a man-in-the-middle attack?
A man-in-the-middle attack is a particularly nasty type of attack in which an attacker inserts themselves in the middle of your connection to a server. While you think you are communicating with facebook.com all of your traffic is actually being routed through a cybercriminals system allowing them to watch every action you take.
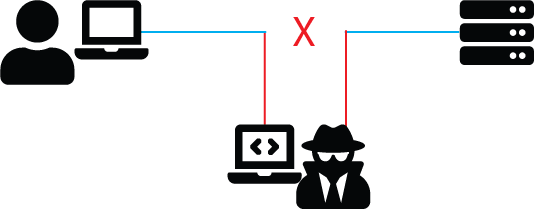
A man-in-the-middle attack can be extremely dangerous because often times the user does not know they are communicating with the attacker and will happily enter their personal information.
Luckily there are a few simple measures you can take to protect yourself against a man-in-the-middle attack.
How to protect yourself against a man-in-the-middle attack
- Prefer sites that offer HTTPS (look for the lock icon in your browser)
- Use a VPN to send your traffic through an encrypted tunnel
- Read and understand browser warnings!
Let us now look at each of these points in further detail. Beginning with step 1, you should always prefer sites that offer HTTPS. Most sites these days are secured with HTTPS so this is not as a big a problem as it once was. However server misconfigurations do occur so always check that a page is using HTTPS before entering sensitive information on a website.

While HTTPS encrypts the traffic between your computer and the web server, a VPN will encrypt all traffic leaving your computer and pass it through a VPN server in the cloud.
Read browser warnings!
Don’t just breeze through browser warnings! Your browser will warn you with a pretty obvious page if something is not quite right with the site’s SSL encryption (HTTPS).
Most of the time this occurs because the web administrator forgot to renew the certificate before the expiration date. The same warning can also occur when an attacker has inserted themselves in your connection and are using an invalid certificate. Ignoring the browser warning in this case would mean game-over for your privacy as the attacker can now see all your traffic as unencrypted plain-text.
While it is easy enough to see if a website is using an appropriate SSL certificate, the next attack requires a little bit more effort on the attacker’s part.
What is a SQL injection attack?
Any application or website that stores information from and about users will likely have some sort of database backend for storing information. Unfortunately, there are many poorly designed forms that do not properly sanitize user input. This can lead to attackers bypassing access checks (such as passwords) or even executing arbitrary commands on the server.
Let’s take a look at an example to see how a SQL injection attack works. For this example we’ll pretend we have a login form that accepts a username and password. If you want to follow along, make sure to download the SQL injection demo repository from Github.
Example SQL injection attack
Ordinarily when the user hits “Login” the application will take the field values, and execute a query that looks roughly like:
SELECT * FROM users
WHERE user_name LIKE ''
AND user_pass LIKE '';Let us see what this looks like when we log in with our fictitious admin user. I say fictitious because surely no real admin has such a simple password…right?
SELECT * FROM users
WHERE user_name LIKE 'admin'
AND user_pass LIKE 'adminpassword';If we get a result we know that user account ‘admin’ exists, and the password is correct.
A malicious password
What happens when a malicious attacker tries to gain access to this form? The need for proper input sanitization should immediately apparent. We can completely bypass the password check with a simple specially crafted password:
' OR 1=1;-- Now our query becomes:
SELECT * FROM users
WHERE user_name LIKE 'admin'
AND user_pass LIKE '' OR 1=1;-- ';What happens now? The WHERE clause on the user_name will continue to function normally, but the real issue occurs when we check the password validity. Since the query OR 1=1; will always evaluate to TRUE, it does not matter what password is entered.
The addition of — after the end of our query is a SQL comment. Everything after the comment symbol is ignored. This is a handy trick for SQL injection attacks as it prevents any potential syntax errors with the rest of the query.
Preventing SQL injection with proper input sanitization
Obviously it is very bad news that the application executes any arbitrary SQL that is submitted. Luckily all it takes is a little of input sanitization and this problem can be alleviated. Sanitizing the previous malicious input gives us the following query:
SELECT * FROM users
WHERE user_name LIKE 'admin'
AND user_pass LIKE '\' OR 1=1;-- ';We see that our imaginary sanitization parser has escaped the leading quote. Now MySQL treats the input as a simple string. This is obviously a very simple example and there are many more ways to inject SQL.
This is exactly why user input sanitization is so important. What if the user wasn’t necessarily malicious? What if their username was d’angelo? How would the application handle that with sanitization.
A SQL injection attack depends on the application containing a specific vulnerability. The next type of attack however, can target nearly any kind of network device and unleash a massive headache for administrators.
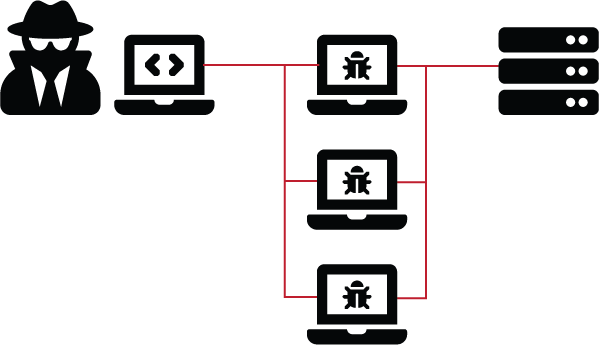
Distributed denial of service: the nuclear option
A distributed denial of service (DDoS) attack attempts to disrupt the operation of a website or service by overloading the system’s capacity through a large volume of erroneous or irrelevant requests. Attackers will often use a botnet , or large network of compromised machines, to carry out the attack. This is where a distributed denial of service attack derives its name. This makes IP based black-listing difficult as the requests are coming from a vast number of different originating IP addresses.
A common protection method against DDoS attacks is to use a CDN that also provides DDoS mitigation such as CloudFlare. Using such a service they can detect and mitigate DDoS attacks as they occur. You may have even heard of the unprecedented DDoS attack carried out by IoT devices against krebsonsecurity.com in 2016. In this attack malicious actors targeted Brian’s site with 10’s of millions of compromised IoT devices, Tgenerating almost 620 Gbps of traffic!
Martin McKeay, Akamai’s senior security advocate, said the largest attack the company had seen previously clocked in earlier this year at 363 Gbps.
What is a password attack?
Hackers may often come across leaked databases of usernames and password hashes. Attackers cannot login with these password hashes directly. With enough time and computing power however, persistent attackers can break the hashes and recover the original password. This then allows the hackers to login to the service that the password protects.
Another method is to attack the login form directly with good old fashioned brute force. Brute force is essentially guessing with the hopes of finding the correct password. Do not be fooled. Brute-force password guessing is still one of the most common ways that attackers compromise accounts.
Rather than trying ever single possible combination of characters, numbers, and symbols, attackers will often start with common password lists. These lists have been accumulated over a large number of breaches, and are often sorted to put the most common passwords towards the top. This significantly reduces the time it takes to crack any accounts using simple or default passwords. You can pretty much guarantee if your password is ‘password’ your account is already compromised.
We used this same method when taking over a router with brute-force. While that example was on a much smaller scale, the attack remains the same.
What is a cross-site scripting attack?
Cross-site scripting (XSS) is when embedded code on one site can take within the users browser. Such an attack is often used to exploit the victim, or steal cookies allowing attackers to impersonate the victim.
Let us take a closer look at how a cross-site scripting attack works. XSS is what is known as a client site code-injection attack. This means that the code is run in the victims browser. But how does the code get there in the first place? Well, unfortunately many sites online today are vulnerable to XSS right now. Popular targets include discussion boards or forum sites. These sites often do not properly sanitize user input before displaying messages and comments. This is all good and well when you have properly behaving users that use only text and funny cat images. But what if an attacker decided to post a bunch of malicious Javascript code rather than a thoughtful comment? This code, if not properly sanitized, could run in the browser of any one that visits that page.
Preventing a cross-site scripting attack
Similar to a SQL injection attack, a cross-site scripting attack depends on a vulnerability in the application. Proper design practices and user input sanitization are key to preventing a cross-site scripting attack.
What is a ransomware attack?
In a ransomware attack a cyber criminal will attempt to infect a user’s machine using a malicious piece of software known as ransomware. Ransomware has quickly become one of the most dangerous and damaging types of cyber attacks in use today. Once installed the software will begin to encrypt the users’ files with a strong encryption algorithm. The ransomware leaves the operating system and vital drivers alone so that the machine will continue to operate. The software leaves a ransomnote for the user. The note usually informs the user that their files have been encrypted and they will need to pay a ransom in order to unlock their files.

Security researchers have found ways to reverse the encryption on many popular ransomware variants. Cyber criminals however are continuing to evolve their tactics on a daily basis and it takes time to decompile and analysis the ransomware in order to even attempt to begin decryption. The best method to protect yourself from ransomware is to maintain a good clean back up. This will allow you to restore your files and not need to pay the ransom.
Perpetuating the cycle
Paying the ransom perpetuates the cycle as cybercriminals will continue to develop ransomware as long as it is profitable.
That is why many security professionals have said that the best way to stop these types of cyber attacks is to not pay the ransom. If the money dries up extorting victims the cyber criminals will look to other methods to finance their activities.
Ransomware attacks focus on larger targets
Ransomware has also become a plight of many small businesses and small municipalities or local governments. These organizations usually have lower budgets for security and lower awareness overall. This makes them easy targets for cyber criminals who can now demand a higher ransom. An individual may consider their family photo collection priceless, but that doesn’t mean they have $10k to fork over to decrypt. A school district whose records were encrypted? Much more likely.
Staying safe. Staying cyber-secure.
While it may seem like an up-hill battle staying secure in today’s evolving threat landscape is all about the mindset. By learning about the most common types of cyber attacks you are arming yourself with the knowledge you need to protect yourself from cybercriminals. Be mindful of the information you give out, and always think about the potential security repercussions of your actions.
If you are interested in cybersecurity you may enjoy our other articles:
- How to Build a Virtual Penetration Testing Lab
- What is Fast-Flux DNS
- How to Install Kali Linux in VirtualBox
- Understanding the Cyber Kill Chain in the Cloud
Also keep an eye out for our follow up articles where we deep-dive these types of cyber attacks in further detail!
One thought on “7 Types of Cyber Attacks That Could Be Targeting You Right Now!”
-
Pingback: How to Install MySQL on Mac (Brew and DMG methods) - Securing Ninja
Leave a Reply