The cyber kill chain defines the lifecycle of a cyber attack and identifies various phases during a system intrusion. Although there are numerous interpretations of the cyber kill chain, the most basic form consists of seven stages. In this post I describe these seven stages of the cyber kill chain and how it applies in the cloud.
Although some interpretations may use slightly different names for the various stages, the overall concept remains the same.
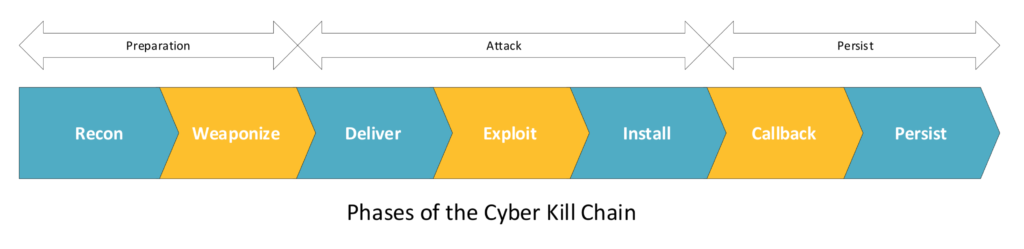
The basic seven stages of the cyber kill chain are:
- Recon
- Weaponize
- Deliver
- Exploit
- Install
- Callback
- Persist
I will now elaborate on each of these stages and how they apply in a cloud environment.
Recon
During the reconnaissance or information gathering phase, threat actors collect as much information about the intended target as possible. This data often comes from external sources allowing the attacker to avoid contact with the target until absolutely necessary.
A motivated attacker will leave no stone unturned when searching for information about a target.
Attackers use a wealth of intelligence gathering techniques and sometimes may spend months gathering information about a target. Careful analysis and application of this information can allow attackers to carefully tailor an attack with a higher probability of succeeding.
Anonymous Recon with OSINT
Open-Source Intelligence (OSINT) is the act of collecting information from publicly available sources. For instance, an attacker may crawl an organization’s Facebook page to identify potential employees. When an attacker collects information from publicly available sources they gain information about a target without needing to interact with them directly.
See my Open Source Intelligence Primer for a more in-depth look at the reconnaissance phase.
The less direct contact between the attacker and the target the less chance of being detected. For this reason, attackers will avoid contact with their target through any direct means until it is time to strike.
Public registry databases such as WHOIS provide a wealth of information about targets including IP addresses, phone numbers, technical contacts and email addresses. Armed with this information, attackers can launch very convincing spear phishing attacks during the delivery phase.
Attackers may also scour social media sites such as Facebook, LinkedIn and Twitter. Doing so may reveal further information about employees, their schedules, and their habits.
Social Engineering with Social Media
Employees are often less conscious of the security implications of posting to social media and other cloud services.
It is not entirely uncommon for a system administrator to inadvertently leak sensitive information when using public cloud services. In fact, a North Carolina State University (NCSU) study of public Github repositories revealed leaked credentials in over 100,000 Github repositories.
With a list of viable emails and usernames in hand, an attacker will then search for matching online accounts. This may reveal passwords available in a recent data breach. Unfortunately many users re-use passwords across many services, and are often slow to change their passwords after a breach.
The explosion of cloud computing has vastly increased the amount of information available to an attacker. Simply collecting all of this information serves little use to an attacker. An attacker must now analyze and weaponize the collected information. From there an attacker can develop a strategy for exploiting any discovered weaknesses.
In the following section I describe how an attacker prepares to strike by weaponizing the information they have collected thus far.
Weaponize
After performing thorough reconnaissance of a target, an attacker will have a pretty good idea of where and how to strike.
In the weaponize phase an attacker builds their ‘cyber weapons’ and prepares to strike the target. If the attack involves deploying malware it will need to be hosted somewhere. Similarly, if the attack involves phishing emails, then the attacker will need to craft the email bodies.
This phase may use information gathered during the reconnaissance phase to develop attacks specific to a target.
Cybercriminals automate too…
One of the greatest benefits of cloud computing is the ease of automation. Of course cybercriminals take advantage of the benefits of automation as well. Automation allows for quickly provisioning infrastructure. This significantly reduces the time between the reconnaissance phase, and the actual strike.
Creation of phishing pages, malware hosts, and command and control infrastructure can all be accomplished in a matter of minutes using common automation tools such as Puppet, Chef, or Ansible.
Attackers also use generic cloud resources to host their command and control infrastructure greatly increasing resilience against take downs.
One recent example I have encountered in the wild is the use of Azure Pages for hosting phishing sites. Hosting phishing pages on a trusted cloud provider such as Azure has the added benefit of providing a trusted domain. Traditional firewalls will typically not catch this kind of traffic.
After an attacker has finished setting up their infrastructure they will deliver their intended payload.
Deliver
This is where the attack begins in earnest. During the delivery phase the attacker delivers the malicious payload to the intended victim. This delivery can take the form of a phishing email, a watering hole attack, a supply chain attack, or even a dropped USB drive.
With almost everything in the cloud these days it seems obvious that malicious payloads and phishing pages are served from the cloud as well.
This can take the form of a cloud hosted download server, or a publicly available file-sharing site. Attackers have used popular services such as Pastebin, Github, or even Pinterest and Instagram to deliver their payloads.
Trusted services, the Trojan horses of the Internet
Using common services such as Google Drive also helps bypass the ‘human firewall’. Users are much more likely to trust a link directing them to a known site with a valid certificate.
Luckily many users are smart enough not to click links directing them to a random domain. However, are those same users as wary of clicking links that lead them to a document in Google Drive?
Attackers constantly refine their delivery techniques. The vast number of different delivery methods grows every day and evolves quickly to take advantage of new weaknesses.
Exploit
After the malicious payload has been delivered it must exploit the system before it becomes active. While an exploit may attack a system vulnerability, an attacker may also attempt to exploit the user. For example, a downloaded Word document may entice the user to activate macros to view the full document.
During the exploit phase the attacker will exploit any vulnerabilities found during the reconnaissance phase. Due to the number of unpatched systems in the wild it is not uncommon for an attacker to have a number of previously disclosed vulnerabilities to draw from.
Occasionally an attacker will take advantage of a previously unknown vulnerability with a zero-day exploit.
Other attacks may make use of browser vulnerabilities with drive-by sites which contain malicious Javascript code. Simply browsing to a malicious website may trigger such an exploit.
Accelerating expansion of cloud computing provides an increasing attack surface with numerous attacks targeting unprotected credentials, weak passwords, and poorly configured or default systems.
Install
Once the initial exploit has taken place the attacker will begin to install their malicious payload. The installation phase usually consists of a series of installations. For example, the initial exploit may download a reconnaissance tool to gather further system information. Depending on the information returned the attacker may then deploy a more specific malicious payload such as a key logger, banking trojan, or crypto miner.
Callback
Cybercriminals do not simply want to exploit systems for the fun of it, well most of them anyways. Instead most cybercriminals want to exploit systems for personal gain. In order to extract information that can be exploited for financial or other gain, the malicious payload must send this information back to the attackers.
This transfer of data occurs during the callback phase. The callback phase is how attackers control their new asset. This connection can be used to extract information, add the compromised host to a botnet, or attack other systems on the network.
Public Cloud Callback
In their ongoing struggle to evade detection, attackers use commonly available public services to mask their command and control activities. For instance, the Twittor project relay’s commands using the Twitter API.
Similarly, the Gcat project executes commands through Google’s Gmail. By using popular public services, malicious traffic is more likely to bypass firewalls, and has the added benefit of blending in with regular traffic.
The use of public services also provides resilience for the attackers infrastructure. Continuing with the Twitter example, all malicious traffic gets routed through Twitter’s servers. This makes investigations much more difficult as the traffic cannot be easily traced back to the attackers system.
Persist
Most attackers will not simply pack up and go home once they have penetrated a network. In the final phase of the cyber kill chain attackers will use whatever foothold they have gained and implement some form of persistence mechanism for long time personal gain.
The longer an attack remains undetected, the longer an attacker can exploit their target.
Once a foothold has been established in a victim network attackers can begin to further exploit the target. This may involve extracting valuable information, defacing websites, launching a denial-of-service attack, or moving laterally throughout the organizations network.
Lateral movement happens very quickly in a cloud environment. With many cloud administrators focusing on perimeter security, private networks within a cloud usually operate with very open permissions. Once a system in this network has been compromised it is very easy for an attacker to compromise other systems in the network.
Attackers use the cyber kill chain…so should you!
In this post I have elaborated on the various stages of the cyber kill chain, and how these stages apply in a cloud environment. When keeping systems secure it helps to take on the attacker’s mindset and understand their goals and techniques. The cyber kill chain describes the series of steps that an attacker may follow. When implementing security for a system it always helps to use a defense in depth approach.
Some form of security can be applied to each phase of the cyber kill chain. For example, limiting leakage of sensitive information to public resources will limit the amount of information available during reconnaissance. Keeping systems patched will make it harder for attackers to weaponize and develop exploits. An effective spam filter will help mitigate delivery of phishing emails. Similarly, installing an effective personal anti malware software can prevent the initial exploit from even occurring, and an effective firewall can prevent a successful callback from reaching the attacker.
I hope this post has increased your understanding of the cyber kill chain in the cloud. If you have any questions, please leave a comment below and I will leave you an answer!
3 thoughts on “Understanding the Cyber Kill Chain in the Cloud”
-
Pingback: Fast Flux DNS: What is it? How does it work? - Securing Ninja
-
Pingback: 7 Types of Cyber Attacks Targeting You Right Now! - Securing Ninja
-
Pingback: How to Use nmap to Find Devices on Your Network - Securing Ninja
Leave a Reply